More and more Australians are turning to virtual private networks (VPNs) as a way to work and connect to remote data storage centers. There are many reasons for a VPN service, but they are not all created equal. Some work well on all devices, and others do not work on a mobile, some keep data logs and some cap your downloads. Often it’s neccesary if you are in remote or public places using public internet connections to ensure your secured, a VPN can help with that. If it’s for a business be sure to get in contact with us for a managed Business IT service in Brisbane.
Here are some tips for how to setup your VPN in Australia. Here are some things to consider when choosing a VPN provider:
- Where in the world is the company and its servers?
- What encryption protocols does it use to keep your VPN safe in Australia?
- Does it limit how much data you can transfer?
- What devices and operating systems the VPN service supports?
Where are the servers
It is important to know where the VPN company and its servers are in the world for two main reasons:
- Access to unavailable websites. For people who want to access websites or content unavailable to them in their home country, it is best if the VPN servers are in that country. For example, if you want to download services based in the US then it is best to choose a VPN service with servers based in the US.
- Privacy concerns. If a VPN is primarily to address concerns about data privacy, then check where the service provider has its headquarters. Wherever a corporate entity is located are the laws the laws they have to obey. Try to avoid countries with mandatory data retention laws like Australia.
Is a VPN safe in Australia?
Whether a VPN is safe in Australia or not depends on the encryption protocols the service provider uses. Here are three encryption protocols to watch out for:
- OpenVPN. OpenVPN uses open source technologies. It has multiple options for configuration and is sure to setup a VPN safely in Australia. Its biggest advantage is that traffic going through the VPN is identical to normal be traffic. This makes it difficult to block content. The disadvantage is that it is not built for many operating systems or devices. You may have to use a third-party app to use it.
- L2TP/IPSec. The Layer 2 Tunnel Protocol is not encrypted. It is the IPSec that encrypts the data making it slower as it converts the data to L2TP and then encrypts it. The advantage is it is easy to use across all your devices.
- PPTP. Point to Point Tunnelling Protocol (PPTP) is one to avoid. Although it is easy to setup a VPN in Australia, it is not secure to use.
- SSTP. Secure Socket Tunnelling (SSTP) is a Microsoft protocol for Windows. It works well and is safe but is not good for using across multiple devices or platforms.
Data limitations and speed
Check how much data VPN service providers allow in their packages. After all, you are paying good money for a service so you want to compare how much data you get and download speeds. You do not want to sign up and find out the service does not meet your needs.
Multiple device and operating system support
Make sure your VPN allows you to connect to any of your devices. Some only allow single device secure connection.
Also, check what operating system the VPN is compatible with. if you have an Android smartphone, Windows on a laptop and an iPad you will want the VPN to work on all those operating systems.
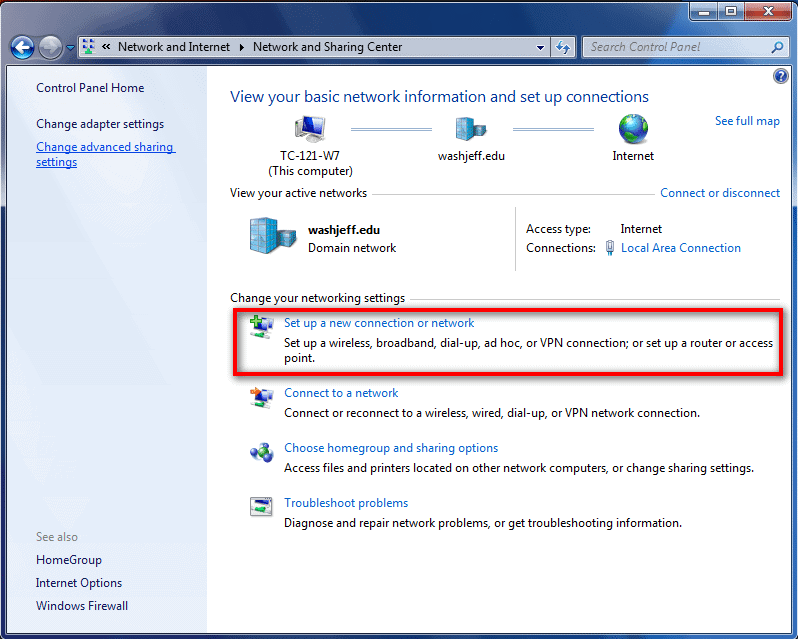
Now you have some idea of what to look for in a VPN, you can find the best service provider to use to setup a VPN in Australia. If you need help setting one up let us know and we can bring our computer service to your home!